1. One to help
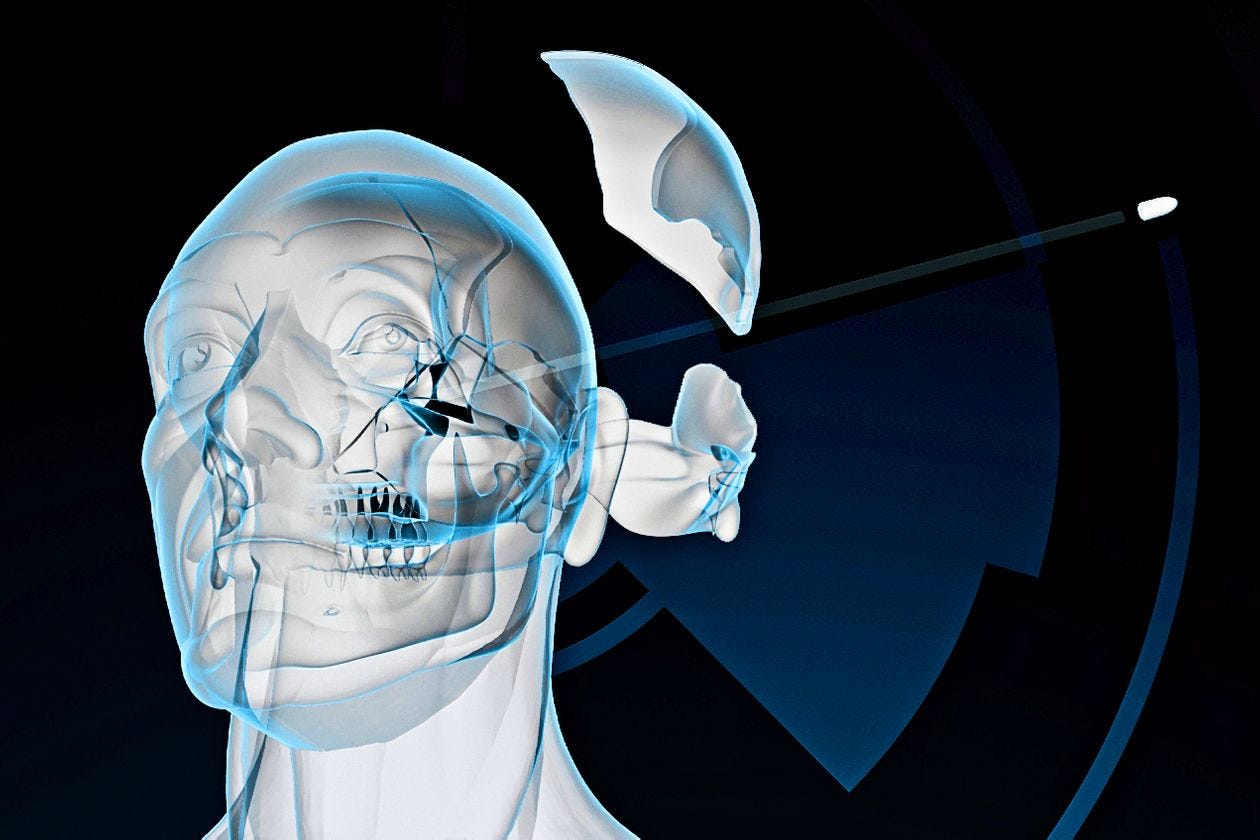
Illustration: Eddie Guy
Researchers around the world are using machine-learning and augmented-reality (AR) to enable coroners to get results without the need for an incision.
Monash University in Melbourne are working with a team to create 3D reconstructions of victims that can be virtually sliced from any direction or angle. They can model the skull of a shooting victim and apply computer algorithms to determine the trajectory of the bullet as well as other critical information.
The method requires a large database of human bodies that have been CT scanned to create cross-sectional images (as opposed to the current two dimensional X-rays). The machine-learning is most effective when it can analyse a large sample of people who have died in similar ways.
Using AR goggles and simulated images, in addition to established forensic techniques, the Victorian Institute of Forensic Medicine (which has built up a database of 80,000 CT scans) reduced invasive autopsies from 80% of cases in 2005 to around 48% now. These techniques are being applied to identify victims of natural disasters where forensic investigators are racing against time.
This technique will hopefully reduce the amount of invasive autopsies required whilst simultaneously improving the outcome for both grieving families and for courtroom evidence.
2. One to be wary of
Regular readers of this newsletter will know of my concern with facial recognition technology. The US Department of Homeland Security (DHS) has now acknowledged that photos on their system, which were part of a facial recognition pilot program, were stolen and released onto the dark web. Your not-so-friendly neighbourhood hacker, calling himself “Boris Bullet Dodger”, managed to access the servers of a DHS subcontractor. When the request for money was refused Boris uploaded an unknown number of files to the dark web.
The report said that 184,000 images from the database were stolen and 19 of them were found on the dark web. Keep in mind, these are just the numbers that were confirmed, many more could eventually be traced. We have no idea how they may be accessed and used.
The issue arose after an employee of the subcontractor accessed the Customs and Border Protection (CBP) system, and moved files to their own company servers. Then old “Boris Bullet Dodger” found his way in and discovered he had something potentially valuable.
This event shows that security around the process of how work is done is just as important as securing your servers physically and virtually. And maybe think twice before gifting anyone your facial identity.
3. One thing to amaze
Your dreams are random experiences that can be wonderful, mundane, or terrifying. We can’t control what happens in our dreams – until now.
Researchers at MIT Media Lab’s Fluid Interfaces came up with a way to insert topics into our dreams. They use a sleep-tracking device communicating with an app to make suggestions which successfully alter the participants dream.
The tech works by interrupting the stage of sleep called hypnagogia. Is is during this stage – the state between wakefulness and sleep – when we suddenly wake up after briefly “dreaming” of falling or stumbling. Apparently, we are open to auditory influences during this stage.
The sleep tracker determines when the user is in hypnagogia and delivers recorded audio cues to the user. Apparently triggering some poor participant to dream about Willy Wonka by playing the Oompa Loompas singing – sounds like a nightmare to me.
Think of the possible benefits: more creative brainstorming, facing your fears in your dreams or even learn a new skill – whilst asleep!
What would you request? I think I might enjoy a dream where I am at a Jimi Hendrix concert in London in the sixties.